I proceed with my article series on using TinyCA2 instead of YaST’s CA-admin tools, whic are simply missing since Opensuse Leap 15.0. Which I regard as a shame by the way …
In the first article
TinyCA2 as a replacement for YaST’s CA-tools on Opensuse Leap servers with TLS/SSL – I
I briefly introduced the user interface of TinyCA2. We used it to create a new CA and a server certificate.
In the second article
TinyCA2 as a replacement for YaST’s CA-tools on Opensuse Leap servers with TLS/SSL – II
we found out where to place the new CA’s root certificate on an Opensuse Leap system to make it available system wide and permanently. We also used the newly created server certificate for the server “myserv.anraconc.de” for all services on this server – and placed the necessary files into “/etc/ssl/servercerts”.
We then discussed the reconfiguration of an Apache2-, an OpenLDAP- and the SSSD-service as examples of how to adapt to the CA and certificate changes. All the required operations on “myserv” were local copy and file editing operations – as “myserv” was the server for administering our new CA, too.
In this third article we, however, look at a second independent server “mymail.anraconc.de” for IMAP/SMTP-services. This server needs its own TLS/SSL-server-certificate. In lack of other tools we shall use scp to deploy the necessary files. I shall further discuss how to reconfigure “cyrus” and “postfix”. Note that these services do not only offer their own TLS/SSL connections to their clients; at the same time they themselves will work as LDAP-clients, i.e. as clients for the OpenLDAP service on server “myserv”. Therefore we must adapt the SSSD-service on “mymail”, too.
Placing a TinyCA2 server certificate on a mail server with cyrus, saslautd and postfix
Our first step is to use TinyCA2 on our server “myserv” to create a second server certificate for the server “mymail” with the common name “mymail.anraconc.de”. This is done exactly as described in my first article for server “myserv”. We export the related certificate and the key files to “/etc/certs” on “myserv” and limit access to the private key file. We export the key file with its password – and strip it off afterwards:
myserv:/etc/certs # openssl rsa -in /etc/certs/mymail-anraconc-key.pem -out /etc/certs/mymail-anraconc-key_new.pem Enter pass phrase for /etc/certs/mymail-anraconc-key.pem: writing RSA key myserv:/etc/certs # cp /etc/certs/mymail-anraconc-key_new.pem /etc/certs/mymail-anraconc-key.pem
Now, we look for some export/import mechanism for deploying “server certificates” from our sytem with the CA administration tool TinyCA2 to other systems. Unfortunately, TinyCA2 does not offer such a client/server feature for certificate deployment within a network. We are forced to transfer our certificates manually 🙁 .
I assume that we have a ssh-connection form our sever “myserv” to our mail-server “mymail”.
myserv:/etc # scp /etc/certs/mymail-anraconc-cert.pem root@mymail:/etc/certs Password: mymail-anraconc-cert.pem 100% 2147 1.5MB/s 00:00 myserv:/etc # scp /etc/certs/mymail-anraconc-key.pem root@mymail:/etc/certs Password: mymail-anraconc-key.pem 100% 1679 1.4MB/s 00:00 myserv:/etc # scp /etc/certs/anraconc-CA.pem root@mymail:/etc/certs Password: anraconc-CA.pem 100% 2504 1.7MB/s 00:00 myserv:/etc #
Note that I transferred the CA certificate, too.
On “mymail”:
mymail:~ # cp /etc/certs/anraconc-CA.pem /etc/pki/trust/anchors/ mymail:~ # cp -r /etc/ssl/servercerts/ /etc/ssl/servercerts.orig mymail:~ # cp /etc/certs/mymail-anraconc-cert.pem /etc/ssl/servercerts/servercert.pem mymail:~ # cp /etc/certs/mymail-anraconc-key.pem /etc/ssl/servercerts/serverkey.pem mymail:~ # chmod 600 /etc/ssl/servercerts/serverkey.pem mymail:~ #
If you read my second article of this series these steps need no further explanation.
Reconfiguring sssd, cyrus and postfix for the new SSL/TLS certificates
First, the sssd-service configuration in the file “/etc/sssd/sssd.conf” has to be updated on mymail:
..... [pam] [domain/default] ldap_uri = ldap://myserv.anraconc.de ldap_search_base = dc=anraconc,dc=de ldap_schema = rfc2307bis id_provider = ldap ldap_user_uuid = entryuuid ldap_group_uuid = entryuuid ldap_id_use_start_tls = False enumerate = True cache_credentials = False ldap_tls_cacertdir = /etc/ssl/certs ldap_tls_cacert = /etc/ssl/certs/anraconc-CA.pem chpass_provider = ldap auth_provider = ldap ... ....
Note that the ldap_uri is the same (!) as on “myserv”! See the last article!
We then change “/etc/ldap.conf” – this enables any clients :
uri ldap://myserv.anraconc.de base dc=anraconc,dc=de nss_map_attribute uniqueMember member ssl start_tls tls_cacertdir /etc/ssl/certs tls_cacertfile /etc/ssl/certs/anraconc-CA.pem pam_password exop pam_filter objectClass=posixAccount ...
Afterwards we change the file “/etc/imapd.conf” – which is a central piece for a working cyrus-based IMAP-server:
.... # LMTP # **** lmtp_overquota_perm_failure: no lmtp_downcase_rcpt: yes # SASL # **** allowplaintext: yes sasl_pwcheck_method: saslauthd sasl_mech_list: PLAIN LOGIN # TLS # **** tls_key_file: /etc/ssl/servercerts/serverkey.pem tls_cert_file: /etc/ssl/servercerts/servercert.pem tls_ca_file: /etc/ssl/certs/anraconc-CA.pem ... ...
You see that we saslauthd as an intermediate link of imap to authenticate (cyrus) users via LDAP (on another server).
Important Note:
The system users “mail” and “cyrus” must get read access to “/etc/ssl/servercerts/serverkey.pem” in case we use exactly one server-wide server certificate/key for all services. Otherwise TLS connections (starttls) cannot be provided for the imap/cyrus-service.
One solution for this problem is to use ACL-settings analogously to what we have done above for user “ldap” on the server “myserv”. See my last article …
For SMTP we also need to change “/etc/postfix/main.cf“:
... .... Client for the local SMTP-Server #--------------------------------- # Changed by admin according to local sasl politics #---------------------------------------------------- smtpd_sasl_auth_enable = yes smtpd_sasl_security_options = noanonymous smtpd_sasl_type = cyrus # Postfix > 2.3 smtpd_sasl_path = smtpd broken_sasl_auth_clients = yes # Local SMTP server as a client for Relay servers #------------------------------------------------ # Inserted by admin - 06.01.2017 #----------------------------------- smtp_sasl_auth_enable = yes smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd smtp_sasl_security_options = noanonymous ... .... ############################################################ # TLS stuff ############################################################ relay_clientcerts = #tls_random_source = dev:/dev/urandom smtp_use_tls = yes #smtp_tls_loglevel = 0 #smtp_enforce_tls = no smtp_tls_policy_maps = hash:/etc/postfix/tls_policy smtp_tls_CApath = /etc/ssl/certs/ smtp_tls_ CAfile = /etc/ssl/certs/anraconc-CA.pem smtp_tls_session_cache_database = smtpd_use_tls = yes smtpd_tls_auth_only = yes smtpd_tls_loglevel = 2 smtpd_tls_CAfile = /etc/ssl/certs/anraconc-CA.pem smtpd_tls_cert_file = /etc/ssl/servercerts/servercert.pem smtpd_tls_key_file = /etc/ssl/servercerts/serverkey.pem smtpd_tls_ask_ccert = no smtpd_tls_received_header = yes ... ...
You saw again that I use saslauth for authentication. But, actually there is nothing to be changed in the saslauthd configuration in comparison to a previously working solution.
Finally, we restart all our services:
mymail:/etc/sasl2 # systemctl restart sssd.service mymail:/etc/sasl2 # systemctl restart cyrus.service mymail:/etc/sasl2 # systemctl restart postfix.service mymail:/etc/sasl2 # systemctl restart saslauthd.service
This should work flawlessly, if we have done everything correctly.
Testing with Kmail and other mail clients from client systems
Before you can start testing with email-clients you need to transfer the new CA’s certificate to your client system’s directory “/etc/pki/trust/anchors/”. Do not forget to import “anraconc-CA.pem” on all other clients that build up TLS or SSL connections to your reconfigured servers, too. And put the CA certificate into “/etc/pki/trust/anchors/” – if your clients are Opensuse Leap 15.x systems.
If you need any direct LDAP client services form your client system to the LDAP service on “myserv” you should take care of the necessary changes in the local “/etc/ldap.conf” and the “/etc/sssd/sssd.conf” !
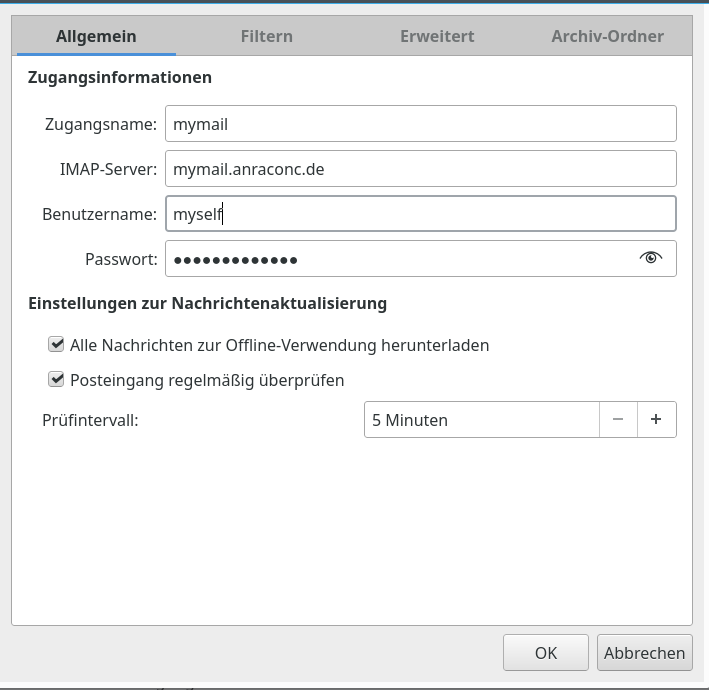
Otherwise you should have a look at Kmail’s or your email’s IMAP account configuration:
Note that you should give the name of the mail server in its FQDN-form to avoid messages on certificates not fitting the server. And:
Clicking on the button “Automatisch erkennen” (or whatever the button is named in English …”Automatic detection ?) should offer you STARTTLS now. If you get any messages about “no connection could be enabled” your configuration of the mail server still has deficits – either in offering TLS/SSL encryption or in its role as a client to the OpenLDAP server. You would have to analyze status and log information of all involved servers then.
You have to do similar things on other email-clients. I was lucky – things started to operate smoothly again on my mail clients.
Conclusion
It really is a problem that the SuSE people did not replace the YaST module for the administration of TLS/SSL CAs and server certificates by a Ruby counterpart with the start of Leap 15.0. Especially as Opensuse works as a basic platform for SLES 🙁 . Also SuSE previously often used a policy to allow for server wide certificates – i.e. one certificate for all services on a server instance. The deployment of such certificates issued by a central CA was supported by an export/import mechanism of YaST, which took care of password-protected keys by stripping of password and setting the right read access rights on the destination servers.
If you want to use TinyCA2 as a CA administration tool you are confronted with a series of challenges – among others the question of access rights of system users to certificate’s key files. In addition you have to place the CA’s root certificate at a proper location on Opensuse Leap systems (/etc/pki/trust/anchors) to
make it permanently available.
TinyCA2 – which I had a look at – is relatively old. The last Gitub change appeared in 2015. Nevertheless it does its job to create a CA, sub-CAs and server certificates (as well as client certificates) – and to revoke them if required. It also offers a simple local export mechanism for certifictaes and keys into standard file formats – as pem. However, this is it.
You need a patch to include SHA256 or SHA512 – which is a must these days. There are some flaws with the simple GUI, but these you can work around related problems – if you know about them. And: TinyCA2 will not help you to deploy the certificates/keys on your server or client systems. Not even a simple import mechanism for a server wide “server certificate plus key” issued by the CA is offered on target servers. So, if you do not want to invest time into your own deployment scripts you may come to the conclusion that TinyCA2 is not suited well for large networks with many servers. In my case I fount it applicable for a dozen servers – but not more. Too much handwork ….
If you consider to use TinyCA2 as a replacement for YaST’s CA administration tools most of your work will be to deploy the TLS/SSL certificates/keys onto your server systems and to reconfigure all services to use these certificates for TLS, StartTLS and SSL connections.
On Opensuse systems the deployment of the CA root certificate within the bunch of permanently trusted CA certificates requires some knowledge about the relevant directory to make the CA certificate available in a central directory as “/etc/ssl/certs” – which may be used by legacy applications. The access rights to a server certificates key file may pose some special problems – you may have to test which system user associated with your services requires read rights.
There are actually several ways how to handle the read access topic for the private certificate keys. I have shown how to use ACLs for this purpose. My recommendation, however, is to use separate certificates and related keys for all services – even if they reside on the same server and despite consequences for your network and DNS configuration due to unique FQGNs and common names. You never know what can happen to a service specific user during attacks. If one certificate/key gets corrupted the others may still survive. Actually, this could be a reason for encapsulating services even more in form of LXC containers. But this is a different story …
Good luck with Opensuse and TinyCA2 !